Crypto and Ransomware: Most Common Tendencies
WannaCry, Colonial Pipeline, LockBit, Change Healthcare — who is actually responsible, and why blaming the payment rail for the crime is the wrong fight.
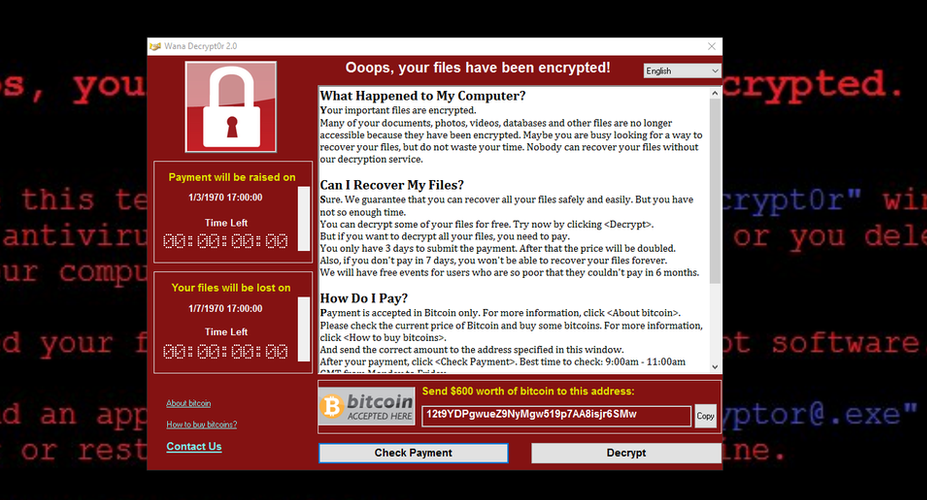
The ransom note is on your screen and you are experiencing this as catastrophe, which is only right because it is. But at the same time, it is somewhere else someone is having it as a customer service call. They wrote a form letter. You even have a team on standby waiting to receive your inquiry. This includes pricing, a negotiation process and where you land if you miss the payment deadline. A few of them got a five-star rating where affiliates review ransomware platforms the way freelancers review project management software.
That chasm — between how the event is perceived from your angle, and how it is viewed from their angle — is where a lot of what makes ransomware interesting actually resides. The technical details, the exploit names, the dollar figures: these are all part of the skeleton. The motion of it is driven by the psychology of what happens to either side of that transaction.
Ransomware isn't a cottage industry. Those who are running serious operations consider themselves entrepreneurs who solved a distribution problem. The product is in place — software that encrypts files and creates leverage — and they just need a way to transform into plausible deniability income without getting pinched.
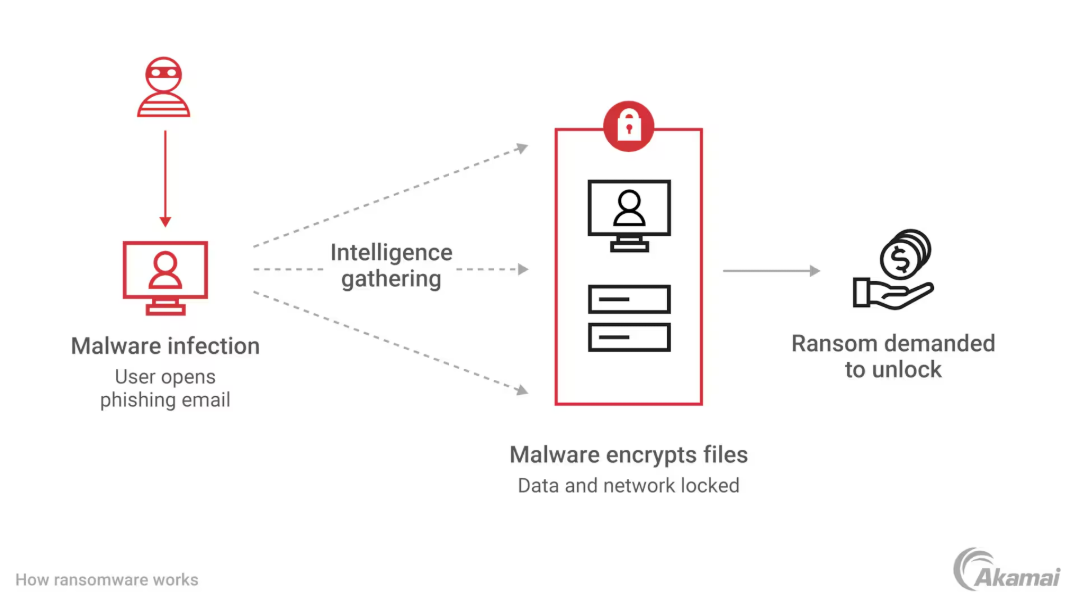
This was solved in an elegant fashion by the emergence of what is known as a ransomware-as-a-service model, which by the early 2020s had become the most prevalent architecture in the industry; the core team builds and maintains both the malware and infrastructure (including cryptocurrency payment processing) whilst taking a cut of every successful ransom paid (typically twenty percent). Affiliates handle the intrusions. The core team never even touches a victim network. Decryption key management is never an issue for affiliates. That's what division of labor is — in extortion.
The Conti cybercrime group's internal communications, leaked in February 2022 shortly after the Russian invasion began and before the group publicly declared their support for Russia, gave an unusually clear view as to how these organizations function. The chats showed HR disputes. Salary negotiations. Technical orders for new hires. Discussions of conditions and retention. An overburdened management team focused on productivity metrics, affiliate recruitment/management and business continuity planning. The Conti operators were operating a software company — one whose output pulverized hospitals and municipalities, but where the lived experience internally was similar enough to any other software company that the admin emails could just be from some startup's Slack. It's a detail that has been inadequately considered. That should trouble people more than it does.
What the Victim Decides
In May 2021, Joseph Blount paid $4.4 million in Bitcoins to the DarkSide ransomware gang. He would later testify to the Senate of this decision. He stated he approved the payment because he did not have a clear idea of how deep the penetration went and how long it would take to recover independently, adding that this was one of the toughest decision of his career.
One thing he didn't say or write, but can be read between the lines of his testimony is how it actually felt inside the decision. That Colonial Pipeline did not pay for a decryption key. It was paying to end a certain sensation — the feeling of being accountable, live, for the shortages of gas that were already spreading along the east coast, for the panic buying, for the lines out front of bidding stations, for the coverage that had reworked a local operational hardship into a national political catastrophe. The $4.4 million calculation wasn't purely rational. It was the price — to say at least to yourself, you tried.
Ransomware operators have to sell this though. Decryption capabilities are the nominal product. It is the relief from an unmanageable kind of pressure: that the consequence of a catastrophe in progress is now riding on a decision you are making at this moment, with maximum uncertainty, on limited information, with shareholders and regulators and reporters watching. Even for organizations that could theoretically restore from backups, the price of that relief turns out to be surprisingly non-trivial. Because rebuilding takes weeks. The pressure is happening now.
The FBI managed to retrieve about $2.3 million of the Colonial payment by seizing the private key associated with the wallet where DarkSide had parked the funds — a recovery that rather belabored the point, with real-world evidence, that Bitcoin pseudonymity does not mean Bitcoin anonymity. It also showed something more troubling: that after the payment was made, Blount briefly felt better, not a rational response to the situation but a very human one. Even if it was baseless, the relief is real.
For the victims who refuse to pay, they suffer a distinct variation of the same psychology. They make a well-reasoned decision only to watch over the next several weeks as (1) this is much more expensive than they expected; (2) their backup and redundancy plans were not nearly as robust as they believed; (3) the estimate provided by the incident response firm engaging in various mitigation efforts was overly optimistic; and lastly at some point there comes an inconvenient truth that forever changes how customers, employees, and regulators evaluate them. The principle holds. The price is more than the planned amount. Say most in hindsight they would do it all the same again — which is what people say when they need to convince themselves that they would.
The double extortion model adopted as standard by the early 2020s — exfiltrate before encrypt and exchange loss of access for public exposure squeeze play — was not a technical advance. It was a psychological one. This is an attack vector that can be fought with backups. The risk of exposing patient records, employee salary data, contracted agreements with vendors or executive email cannot be mitigated by any technical controls. It does something different: not continuity of operations but reputation, privacy and the trust that depends on both. It was the attackers knowing their product better than they did.
Geography of Impunity
LockBit ran by operators that were far from being unknowns among law enforcement. In the last month of a massive, coordinated international effort — led by the UK National Crime Agency — to subdue LockBit's infrastructure in February 2024, named its administrator: Dmitry Khoroshev, a Russian citizen age thirty-one. They published his photograph. Listed his assets. The U.S. Department of Justice disclosed an indictment. OFAC imposed sanctions. It was essentially the complete international wanted poster.
Khoroshev remains at large. He resides in Russia, where the country does not extradite its citizens for cyber crime if non-Russian systems are affected. This is the way in which the entire ransomware economy operates by design.
Traditionally, Russian law enforcement's one simple rule with respect to ransomware has been: targets in Russia or its sphere of political influence are untouchable; anywhere else on the planet is not really a priority. Cyrillic keyboard detection was incorporated into early versions of the code used by the Conti group: if a victim's keyboard layout was Russian, it would trigger to not execute. This was not patriotism. It was a compliance mechanism. The group was managing its relationship with a government that would allow the operations to continue provided that they remained within geographic confines it deemed acceptable.
The implication of this is straightforward: the architects who write policy responses to ransomware in Washington, Brussels, and London are doing so responding to an industry whose principals are almost always out of reach. All this adds up to make too much sense: The arrests that do occur — a few rogue affiliates in Poland, some REvil members arrested in Russia shortly during a period of uncharacteristically warm relations in early 2022, the occasional American or European operator who misestimates their local exposure are an outlier on the fringe of the bigger ecosystem. Where the core is (and always has been).
This accountability geography drives everything else in the policy conversation. If the response you have access to does not including reaching those responsible, you redefine what counts as a response. Washington is reacting with a tool called regulatory cryptocurrency. There are also mandatory security standards for critical infrastructure available, but they come slower; provoke more political pushback; and require confronting the reality that partly this is the government's fault — that federal agencies ran networks with known vulnerabilities for years, that regulatory frameworks for critical infrastructure security were insufficient, that what is happening now partly as a result of choices made by the same institutions proposing to solve it.
It's cleaner to blame the payment rail.
Legislator's Moment
That kind of congressional hearing, which invariably happens in the wake of a major ransomware strike against a piece of critical infrastructure. The affected CEO testifies. They are then continually questioned about why they paid the ransom. They say they were told to. And they are questioned why they did not have better backups. They can explain that their backup systems were only partially corrupted, or that restoring them was not practical with the time constraints at hand. Then they are interrogated about the cryptocurrency. They say something deliberately ambiguous, which is how they stay out of trouble with the lawyers.
It would be inconceivable to think the legislators asking these questions are uninformed. They receive extensive briefings. What they are doing is different from fact-finding: they are shaping a story that the problem has an identifiable, explainable source to be understood by their constituents — and that what they propose to do legislatively to respond to this cause counts as action on ransomware.
In the context of legislation, cryptocurrency is an issue capable of solution. It's an industry contained in their jurisdiction, with lobbyists they can dispute with, the kind of regulatory requirements they can broaden, and tangible metrics of regulatory activity that goes into a newsletter. The kind of visible output that you get from attacking the hackers directly through war or cyberwar cannot happen if you are pursuing the actual operators via foreign policy, intelligence cooperation and extraterritorial legal pressure.
For years, the cryptocurrency industry has made the case that cracking down on crypto will not stop ransomware — because ransomware existed before Bitcoin, because operators would just use other payment channels, because the real criminals live in countries with no respect for American financial regulation. This argument is correct. And, because being right is not the same as effective in a political context — where it needs to be effective most of all — it has persisted in its ineffectiveness. It's a function of providing something that the persons in room are able to use.
BlackCat behavior around Change Healthcare in February 2024 provided an illustration of a completely different problem, which regulatory frameworks are not meant to address at all. BlackCat received around $22 million from Change Healthcare's parent company. Finally, BlackCat exit-scammed: the operator made off with the money and closed infrastructure, leaving his own affiliate working for nothing. The affiliate frustrated about this, began threatening to release the stolen data anyway. The ransomware operators have scammed their own criminal cogs. So for that specific layer of the problem you don't have a good framework with the policy conversation itself.
What the User Carries
The simple people holding crypto for use cases — stablecoin transfers, DeFi positions, remittances and everyday business — they have a special flavor to the ransomware conversation that is not widely explored. They are the ones that actually pay for regulatory responses to crimes they did not commit, and from which they gain no benefit.
It creates a sort of background defensiveness in crypto communities that becomes apparent whenever ransomware hits the news. A person sending USDT for a lawful commercial transfer now finds themselves next to a criminal organisation that they have no involvement with. The team issuing a protocol recounts once more to the world why smart contracts are not responsible for how they are used in ransom transactions. Because of what is done elsewhere in a different country by different people through completely different transaction flows, the end-to-end experience of using cryptocurrency for legitimate purposes becomes more surveilled and cost prohibitive.
The defensiveness is often self-defeating — it comes off not as sincere but tentative, and those on the defensive sometimes overstate their argument in a way that invites dismissal. But the rage underneath this is quite real. You are asked to feel frustrated about paying costs created by a reaction to someone else's criminal behavior, and of course the people who create those costs don't need to justify them in their calculations because the people incurring the costs are not among the constituents whose needs they are addressing.
There is a more intimate view of this, relating to how human beings who own cryptocurrency rationalize their presence to other folks. They distinguish between things that seem obvious to them and opaque to their interlocutors. They compare why dragging a business transfer over a public blockchain is not like using it to send ransom to a hospital. The explanations are correct. It's very tiresome to keep making them, but it's a difference that only those people who don't care — or don't understand — will appreciate.
WannaCry itself teaches us something on this. The attack caused actual damages in the hundreds of millions across the NHS, Telefónica, FedEx, Deutsche Bahn and many others. It actually netted only tens of thousands of dollars in real ransom, because the operators relinquished control over how many victims they could realistically process decryption requests for. A twenty-two-year-old named Marcus Hutchins shut down the malware by registering a previously unregistered domain against which the code was checking, tripping what appeared to be a kill switch built into its creators' designs while working from his bedroom in Devon. The geopolitical narrative was that a weaponised NSA exploit had targeted global infrastructure as part of a struggle that had literally nothing to do with Bitcoin. What remained in the public consciousness was: hackers were asking for Bitcoin.
Why It Continues
In 2023, ransomware payments tracked by Chainalysis surpassed a billion dollars — the first recorded year for which that total crossed that threshold. Payments fell by about 35 percent in 2024, due partly to law enforcement action against the biggest groups and partly because victims had become wiser at saying no. Neither of these developments indicated the underlying conditions were being resolved.
LockBit disrupted, its infrastructure seized, its administrator named and sanctioned — and back to partial operations days later. For more than six months from mid-2022 onwards the FBI infiltrated Hive, stealthily handing victims free decryption keys as the operation ran on until January this year when authorities seized some of its infrastructure. By the time of the 2023 mass-exploitation of MOVEit Transfer, Cl0p had completely pivoted to unencrypted data exfiltration — ransomware without encryption, no files to decrypt but only someone else's networks breached and having their data stolen and a good reason for any criminal actions taken against them. The actual industry snaps to adapt faster than the policy response moves — the security firms have direct incentives to adapt, where the scoring policy has different incentives.
Offline tested backups, multi-factor authentication, patched systems, network segmentation, endpoint detection are all tedious but straightforwardly un-glamorous entries in the much better known security infrastructure that would actually lead to reduced incidence of attacks. That does not prevent the existence of ransomware operators. They increase the cost of every attack to the extent that many victims live and do not pay. They need ongoing organizational discipline and open-ended funding commitment, which is a tougher pitch than a regulatory move that gets things moving in front of cameras without anyone having to pay for something that creates no measurable output while running.
Banning cryptocurrency doesn't secure hospitals operating unpatched software on flat networks. The payment mechanism is one piece of a system where multiple structural cracks coalesced to create the result. The less difficult it is to get at those other failures, the more attention it gets.
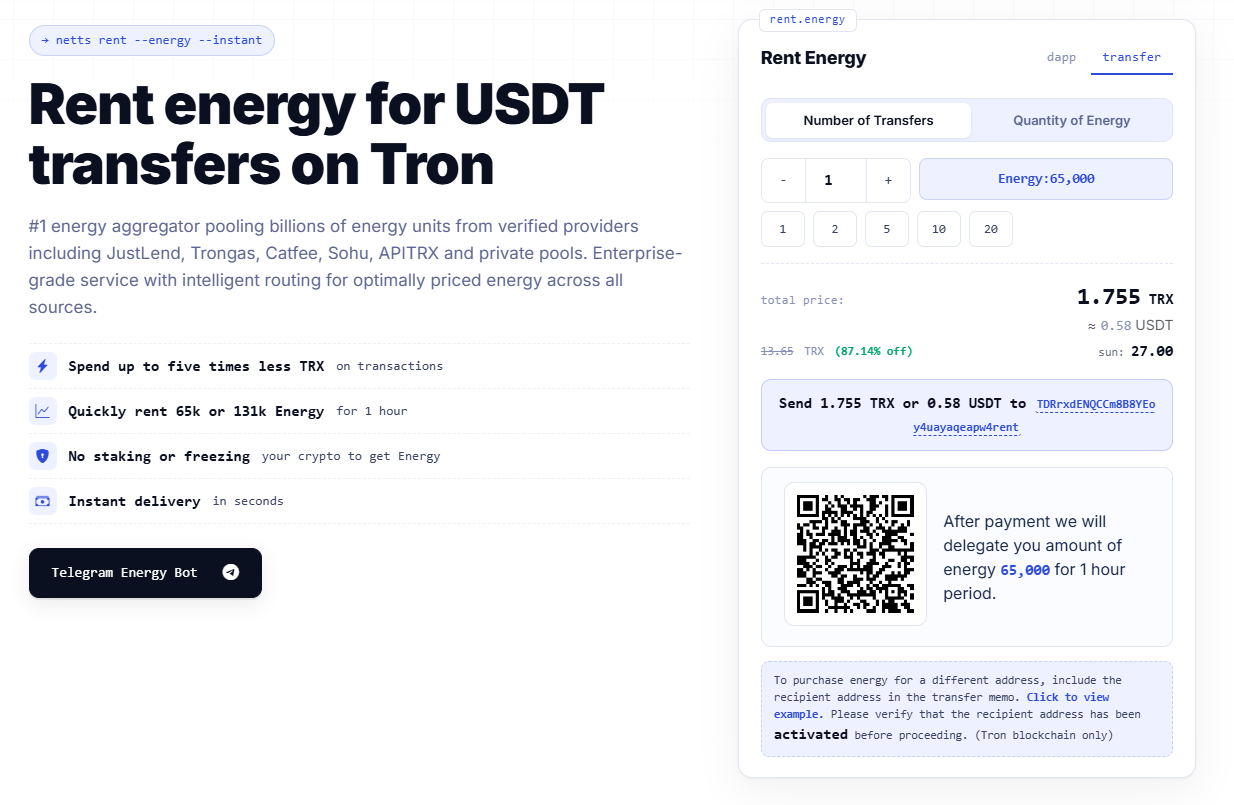
For anyone using stablecoins on TRON — for reasons unrelated to any of this — Netts.io consolidates live Energy pricing from mid-level providers JustLend, Trongas, Catfee, Sohu, APITRX and an average pooled private provider to find and send any required transaction amount to the lowest available TRON Energy price in real-time: currently as low as 25 sun per Energy unit — around 75% cheaper than defaulted TRX burn rate with immediate delegation of transactions and without needing to stake/freeze any TRX. It could be accessed through a simple Telegram bot without a web interface. Whether or not the use context of any given transaction has something to do with ransomware is not a question that the energy market can answer. At least, it deals directly with the cost of the transaction.