Pseudonymity vs. Real Anonymity in Crypto
Coinbase's 12,000 annual law enforcement requests, Tor timing attacks, the Silk Road founder caught via a forum post — what it all means for your privacy.
The pitch that crypto is free money and not amenable to anyone who might care where it goes has persisted longer than it has any right to have. It taps into a real instinct — the need to manage your own money without institutional approval or oversight — and is not wholly incorrect. But it has been wrong enough in enough high-value ways that treating it as a reliable expression of privacy promise has been costly for many people who trusted it more than the evidence justified.
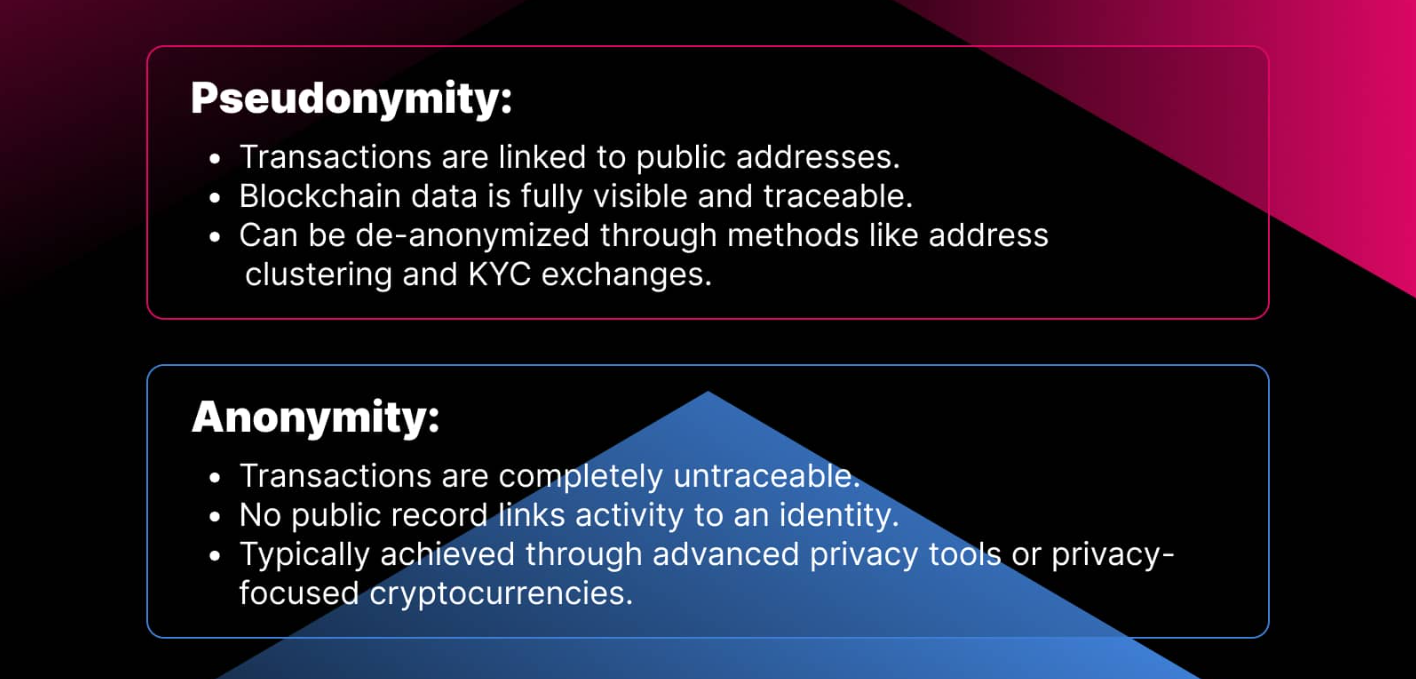
Begin with the simplest fact: The bitcoin blockchain is a public ledger. All transactions performed on the network are permanently visible to everyone and no access controls exist. If you have a wallet address — and exchanges routinely connect wallet addresses with real-world identities through KYC data, IP logging, blockchain analytics, and good old fashioned internet sleuthing — you can follow every transaction that wallet has ever made or received. Not approximately. Exactly. The amount, the timestamp, the counterparty addresses and every subsequent flow of funds from that point backwards and forwards through the chain. It is not an exploitation of a feature that governments take advantage of; it is the design of the technology. The same decentralization that may make Bitcoin censorship resistant also makes each individual transaction auditable forever, publicly.
This architectural reality has been leveraged into a business by Chainalysis, Elliptic, and a dozen firms using the same model. Reactor is a software platform developed by Chainalysis that has been deployed in over 150 government agencies worldwide and has played a role in the recovery of over $12.6 billion in seized cryptocurrency. At over $15 billion, the DOJ's October 2025 seizure of funds tied to pig-butchering fraud was the largest single crypto seizure in history. It is an industry so experienced in industrializing on-chain tracing that when analysts say that 85 percent of U.S. law enforcement now has access to blockchain analytics tools (up from 55 percent in 2020), they are describing a reality where the original privacy assumptions made by early Bitcoin adopters could make for poor daydreams. The blockchain does not lie. It records. And there are people out there who can read it, and they've gotten quite good at doing so.
That does not mean that crypto privacy is impossible. Which is to say, the default is not privacy; it takes a deliberate, technical-focused and constant effort to reach something resembling real anonymity — all while constantly battling adversaries who are also getting steadily more sophisticated each passing year.
Difference Between Private and Invisible
True internet anonymity is not a destination you arrive at. This is a practice you have and one that has many more modes of failure than success — it mostly takes place unsighted, often with consequences only visible once the damage is done.
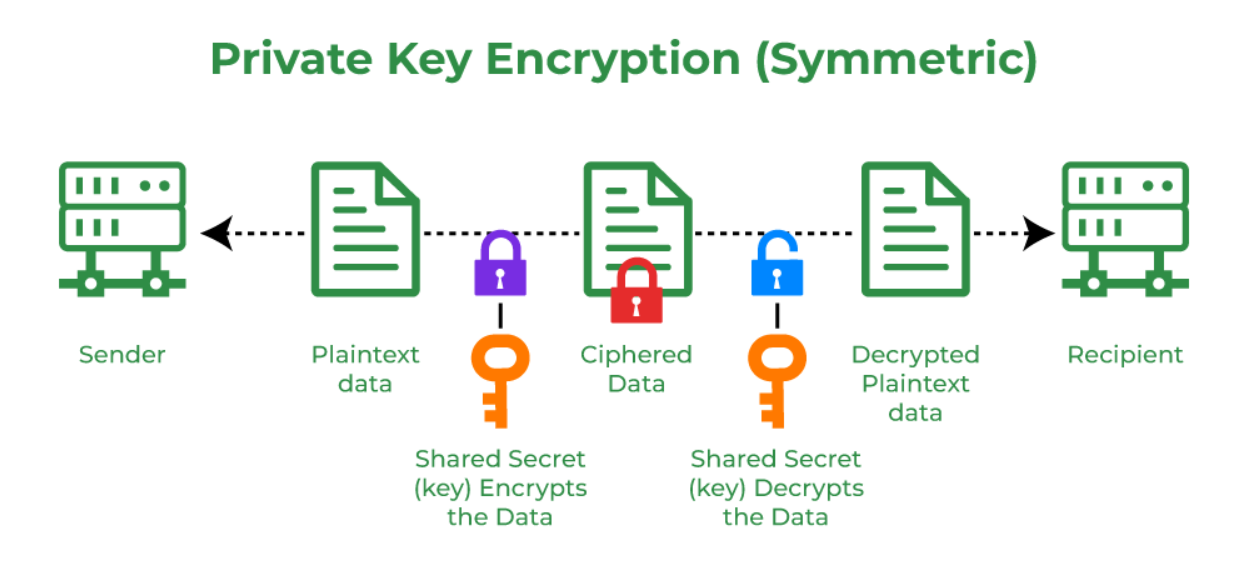
Most people reach for a VPN as their starting point. It is pretty straightforward to see where this rationale comes from: your ISP can see your traffic, an ISP can be served with a legal request and made to hand over your data, therefore if you send all of that traffic through an encrypted tunnel to another server, smokescreen. What it really solves is a much smaller piece of the puzzle. According to this definition, a VPN hides your actual traffic destination from your ISP (unless the software hosted on the VPN provider's servers keeps some useful log). It does not delete your wallet address on the blockchain, where all transactions are public regardless of their originating IP. This will not stop the exchange you bought your crypto on from logging your identity. This will not stop browser fingerprinting — the way by which sites identify users based solely on combinations of hardware, software, timezone, language settings and installed fonts that are statistically unique without any cookies needed. This does not protect you from a VPN provider that keeps logs and responds to legal requests, something well over 100 of them do even if their marketing copy would suggest otherwise.
Tor is a solution that solves some of the routing problem, routing your traffic through multiple relay nodes in such a way that no single point on the chain can see both who you are and what it is you are accessing. It was for years the gold standard of network-layer anonymity, and remains so for many purposes. But it too has limits. In late 2024, German authorities showed that timing analysis — which consists of tracking the flow of packets coming into and out from the Tor network — can de-anonymize users when investigators have control over sufficient relay nodes.
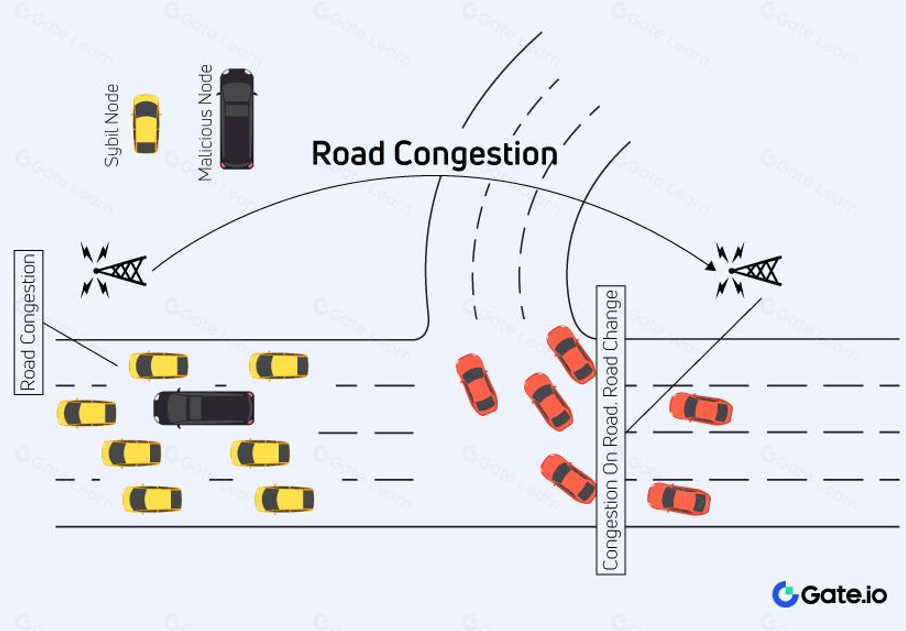
State-sponsored nodes were introduced into the Tor network by a massive Sybil campaign that ran in 2024 and 2025, which was capable of performing precisely this kind of activity. The arrest of Ross Ulbricht, founder of the Silk Road, was not a failure of Tor. They tracked him down because an FBI investigator traced the username "altoid" from a forum post on Silk Road back to a Gmail address that was created years earlier. Years earlier in a moment of thoughtlessness, he had linked his real identity with his operational persona long before it mattered.
Instead of trying to solve it at the network layer, privacy coins tackle the problem at the protocol level. Monero introduces privacy on a transaction by transaction basis with ring signatures — that is, the signature for each transaction is derived from 1 out of 16 possible senders drawn from a pool of decoys — and stealth addresses generated specifically for each incoming payment to the recipient which ensure that a receiving Monero wallet can not be linked to payments received. The result is a transaction that, in theory, is virtually untraceable without some outside input from something on the very blockchain itself. Chainalysis has asserted that they can find Monero users because of a network layer attack (rather than an on-chain one), where they monitor the IPs of everyone who broadcast nodes under their control, but again, this can be avoided by running your own node or routing through Tor. In contrast, Zcash provides for optional shielded transactions using z-addresses and zero-knowledge proofs with no information to determine if their previous or next transaction were made by a specific sender or recipient, referring to the amount being transferred. Just under a third of Zcash supply now resides in shielded pools, compared with only 11 percent at the start of 2025 (though the opt-in model means that many users never deploy any privacy at all).
For a while, mixers and tumblers — services that aggregate money from different users and award roughly equivalent amounts in return to hide transaction activity — were the go-to path for on-chain anonymity. Their legal status has collapsed. In April 2024, three founders of the Bitcoin mixer service Samourai Wallet were jailed on suspicion of money laundering and operating an unlicensed money-transmitting enterprise. Rodriguez got four years; Hill five; both sentenced in August 2025; OFAC sanctioned the Ethereum mixer Tornado Cash in August 2022, only for the Fifth Circuit to strike down those sanctions in November 2024 and OFAC to formally remove the sanctions on it in March 2025 — but Roman Storm cofounder awaits federal trial still.
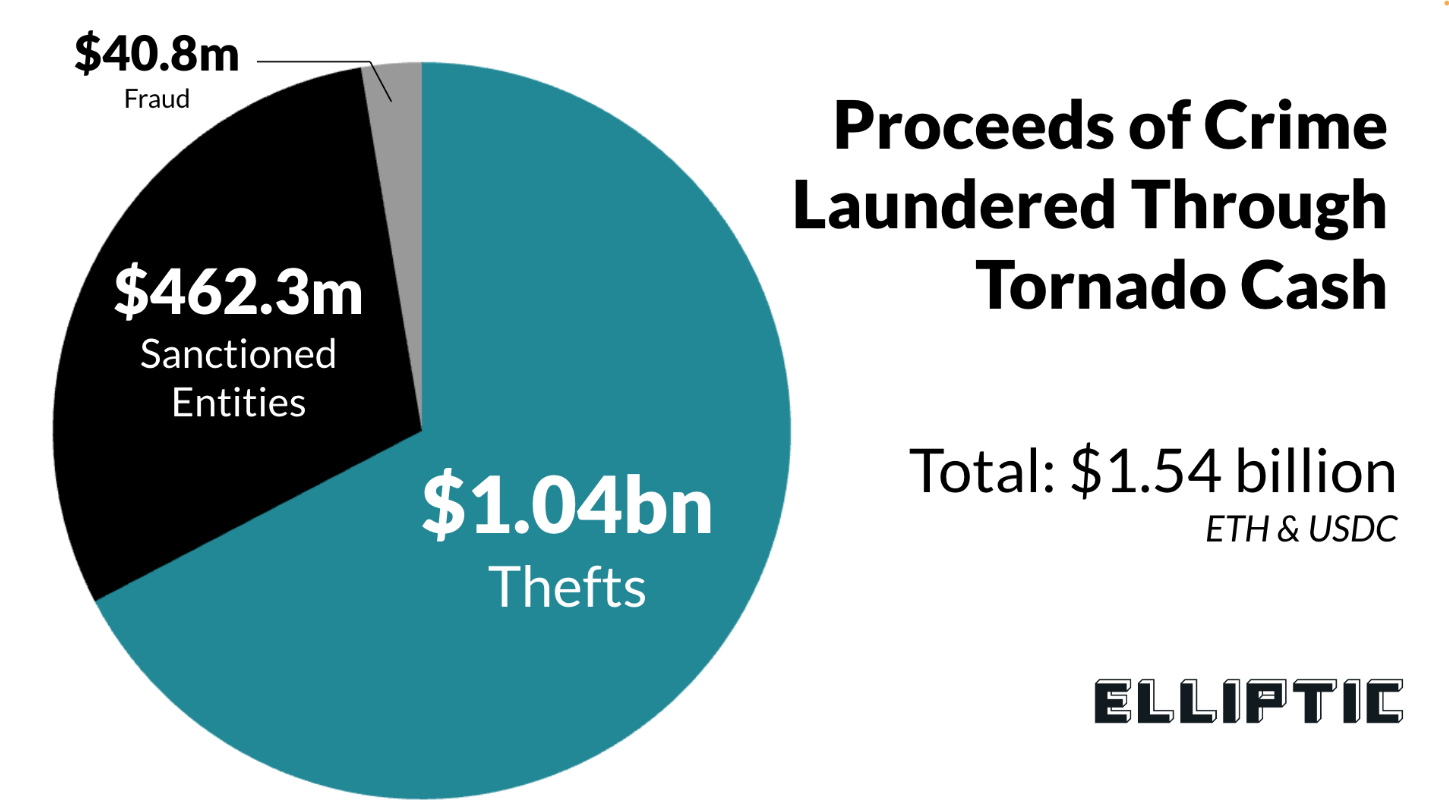
This does not change the technical efficacy of any given underlying approach, but ensures that running or using mixing services has a legal risk that must be considered in any realistic assessment of on-chain privacy tools.
We now have a realistic idea of what "privacy in crypto" can look like for a cautious and technically knowledgeable user, which is something of an amalgamation of:
A non-custodial wallet that has never been connected to any exchange or KYC-associated address.
Monero or Zcash shielded transactions for the assets that want privacy.
A Tor or similar network routing tool together with a self-hosted node that allows non-broadcasting of your IP.
Physical and operational discipline around the devices and environments from which you access or conduct transactions involving cryptocurrency.
Separation of identities, wallet addresses and communications accounts, from any public persona representing the activity.
Those layers are gradually less risky. None of them eliminates it. And the conjunction is so much to ask that most who think they are anonymous have failed to keep all of it continuous.
Pseudonymity's Comfortable Lie
This is where the most pernicious damage from marketing crypto anonymity lies — conflating pseudonymity (use address rather than name) with real anonymity, which requires that whatever connection exists between person and address be permanently and provably broken.
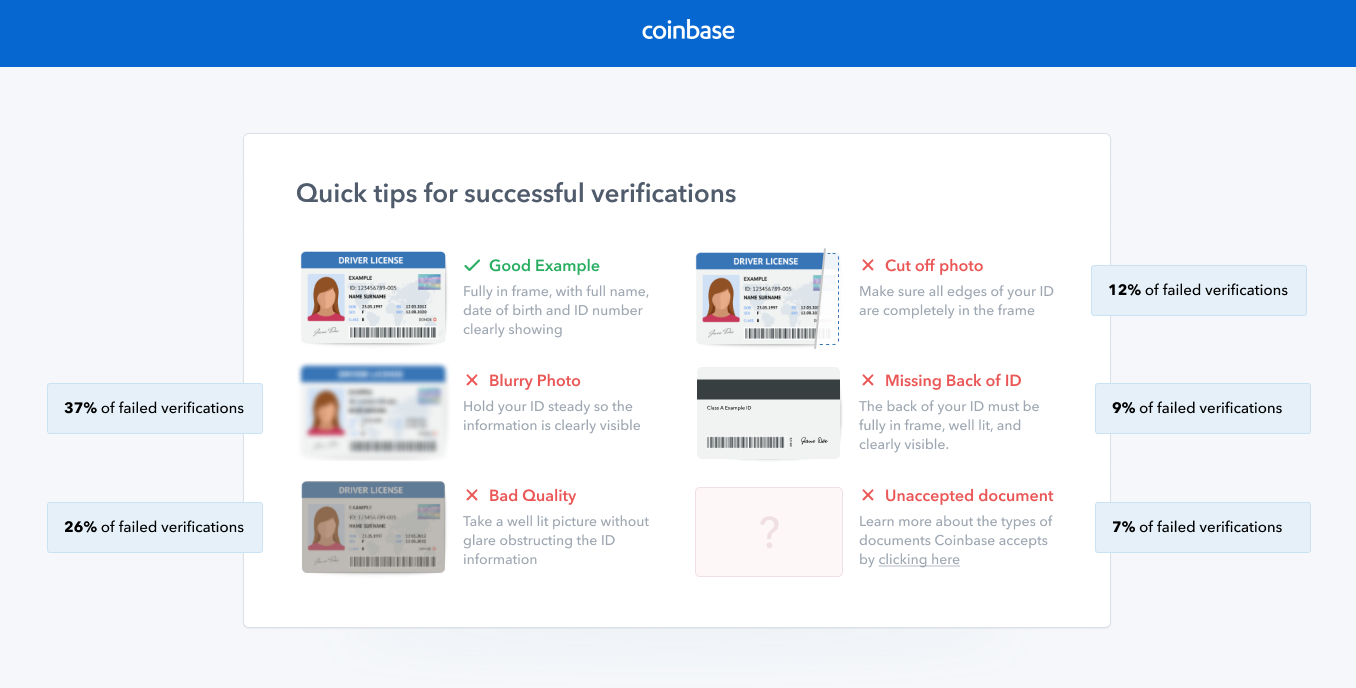
The majority of crypto platforms that users engage with, are from an information protection perspective, practically indistinguishable from traditional financial institutions. Coinbase has a compliance team that was literally just built to handle responding to these kinds of inquiries, and between Oct 2024 - Sep 2025 they received 12,716 law enforcement requests — an increase of 19 percent from prior year. All the big exchanges, including Binance and Kraken that have offices in regulated countries, hold full KYC records on every user along with those they are legally required to share with government agencies.
As of an October 2023 update to the FinCEN Travel Rule, parties sending or receiving $3,000 or more in a transaction are required to record and provide the sender and recipient information upon request. Moving funds between accounts on a large exchange is not in any sense a privacy act — it is the exact opposite of one.
This matters as a practical ceiling of crypto privacy in real-world use cases, which is the on-ramp and off-ramp problem. So if you bought your bitcoin through a KYC exchange with your bank account, and the address of your wallet is already tied to an identity with whom you previously spent (or traded) on the chain, then you cannot actually have private cryptocurrency: eventually you'll need to turn it back into money that can pay rent. Every step in that process creates a record and those records tie together. So-called blockchain analytics firms trace precisely these pathways — the transfer from KYC exchange to self-custody wallet to privacy tool back to liquidation point — so reliably that just an instance of using a mixer in some jurisdictions is enough of a red flag for concern by compliance.
If you purchased the hardware wallet through Amazon with your credit card and it was shipped to your home, that is not anonymity. Your supposed-to-be non-KYC self-custody wallet could have been funded by an exchange withdrawal, linked trivially via compliance records from that exchange to you. The privacy coin which you acquired on a decentralized exchange might be purchased with earnings from an address linked to your identity in addition via way of means of following a chain of transactions that took an analyst 4 steps — positively — to follow. Pseudonymity is the name written on a piece of paper turned face down, sure, you can conceal the address but that sheet of paper still exists; it's there, and if someone is motivated enough to lift it they're going to do so.
It's worth noting TRON actually doesn't fit into this position in this picture. Data from Chainalysis shows that in 2024 TRON made up 58 percent of illicit crypto transaction volume, alongside Ethereum and Bitcoin with 24 percent and 12 percent respectively, with the large USDT use case for this network being reflected by the size of its apparent transaction volume but also partly a result of the fact that high-volume low-fee stablecoin transfers at scale attract a wide range of different types of transactions. This does not make TRON illegal by definition either, and it is no different from cash being considered illegal since drug dealers use it. That reflects the volume is in this network. The operational question is decoupled from the compliance provision: users who use TRON Energy to conduct low-cost USDT transfers without burning any amount of TRX are free to do so, as efficient network usage is available to anyone and can be achieved via TRON Energy bot usages with an arbitrary implementation that require no specific technical requirement.
Leak You Never Expected
Privacy is often not lost because of the technical precautions. They are the manifestation, the artful veil. The human layer — the invisible one — tends to have a better attack record than any public surveillance agency.
Ross Ulbricht's case is the classic example, but it's not alone. The trail of the Bitfinex hackers — Ilya Lichtenstein and Heather Morgan — involved moving 119,754 Bitcoin, stolen in the 2016 exchange hack, through a chain of wallets, mixers, darknet markets, and exchange accounts that took investigators years to follow. They had conversed about the funds over email, kept private keys alongside related files, and in Morgan's case made it no secret that "Razzlekhan," part-time rapper and entrepreneur — and connected to the wallet infrastructure — had built an extremely public persona online. Lichtenstein was given a rather more modest sixty months in November 2024. Morgan received eighteen. They were not discovered because law enforcement was technically smarter than them. Because they answered that we have the digital equivalent of talking about what you did, and they did.
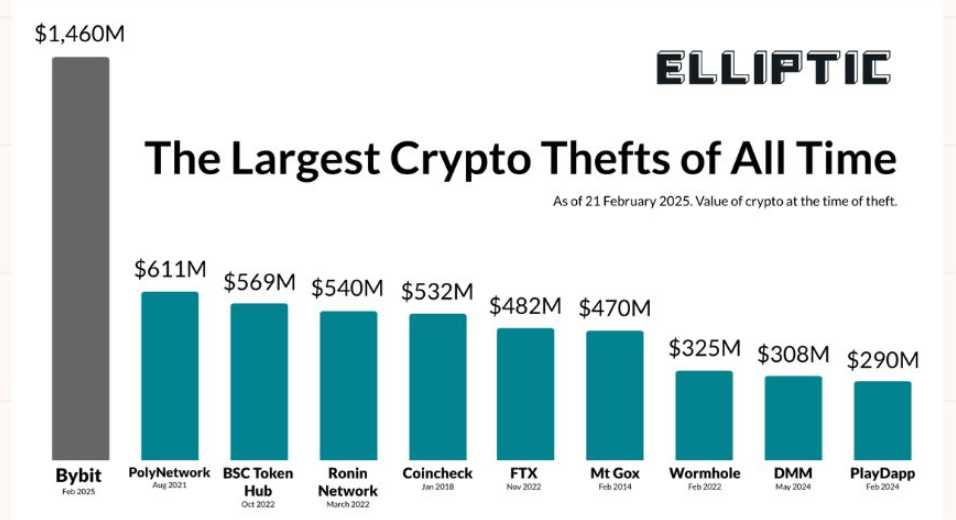
Social engineering is the easiest and most successful privacy attack that requires no technical ability whatsoever. The attacker only needs to have access to a talkative person. The Bybit hack of February 2025 — 401,000 ETH, approximately $1.5 billion — was conducted through a phishing attack that targeted the Safe wallet interface used by Bybit employees. This initial access was not gained through any form of breaking cryptography. This was collected using a spoof interface to get somebody to sign a malicious transaction. The latest 2024 increase in impersonation scams — up from 1,400 percent — and the release of AI training sets designed to reproduce the audio and video of known contacts has made this social engineering vector more powerful than ever.
Under-appreciate the inner circle problem in particular. Even the vast majority of people serious about crypto privacy have told someone. A partner, a friend, a family member, a colleague. That person told no one. Probably. They had spoken over a service that encrypts messages when sent, but not on the user device — at rest. Assumedly when the phone was close to other electronics, connected to the same set of networks and perhaps near a smart speaker. A threat model that considers your wallet infrastructure, but not the human layer of that infrastructure, is not a complete one.
This is not an argument for paranoia, nor for silence. It is an observation that the burden of being able to preserve any kind of meaningful privacy multiplies each time a communication channel is added, each additional person told, every acceptable looking convenience trade off that actually probably does look fine. Wallet privacy is easier to preserve than the privacy of its surrounding conversation, and it is the underlying conversations that tend to come out in put forward process.
Ninja That Never Goes Away
This idea of the untraceable crypto user — flowing funds through privacy coins, tweeting via encrypted channels while leaving no footprints on any surface, it has always been more aspirational than operational. And while the technology for actually useful privacy is hardly more difficult than encrypting your texts and emails, it only works decently most of the time for a small number of extremely disciplined practitioners. Those not fully burned face a continuum of pseudonymity: better than having your name affixed to a bank account, worse than having obscured identity and somewhere in between that space according to how many resources have been committed and how much sheer luck has endured.
The battle between identity and anonymity in a world where no network packet can be obscured, every transaction is recorded immutably on the public ledger, and the organizations determined to identify you (with both the legal right to force disclosure from all of the services that you trust with your private information and the forensic software capable of tracing flows across hundreds of ephemeral addresses) is never ended and cannot be conclusively possible. In reality, your goal shouldn't be to become invisible. It is the expense of identification reaching an untenable point: that the investment required to make that identification outweighs what is likely to be gained. That threshold, for most people is attainable. Absolute certainty is not.
The issue is that the much more pragmatic, and actually used approach among the vast majority of serious practitioners is operational discipline over time: properly separating identities, leaving as little on-chain footprint possible, transacting through hard-to-observe parties, minimizing knowledge of what anybody knows to persons who require to know what to a minimum. It is not glamorous. It's maintaining, not arriving. The ninja analogy teaches readers in the wrong way — no, you are not aiming for show stopping stealth, but for an extraordinary lack of things to draw attention from an observer.
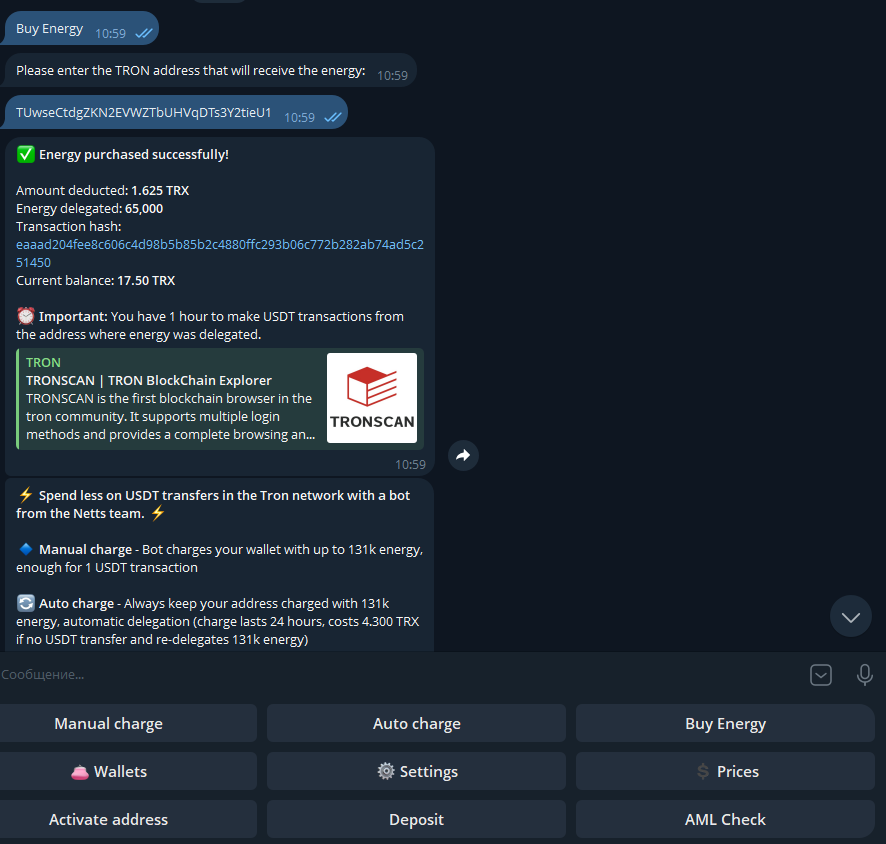
The Netts Energy Charge Bot nails the network-cost side of things directly in Telegram — if anyone's TRON USDT activity crosses that work efficiency line then it allows you to buy Energy on demand before a transfer and charge only what gets used — currently at off-peak rates 65,000 Energy costs around 1.6 TRX, enough for one USDT transaction on average with an auto-charge mode keeps an address loaded up automatically. While some users might consider this a choice between burning TRX and getting TRON Energy with the bot, it is more of an optimization in terms of cost than privacy; but for anybody running a disciplined TRON trade-play truce, it is simply the kind of low-friction operational detail that prevents a clean setup from becoming an expensive one.